Par c@c
Votre connexion devra être configurée avant. Tous les codes du tuto sont à taper dans une console, et vous devez être root (administrateur) pour exécuter le firewall (tapez su, puis le mot de passe root).
Tout d'abord, vérifiez la version de votre noyau :
uname -r
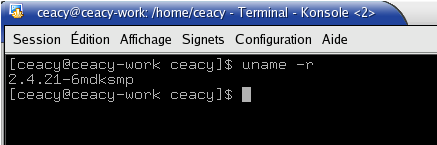 |
En effet, iptables est intégré dans le noyau à partir de la 2.4 (les 2.2 utilisent ipchains). Si votre noyau est un 2.4 ou supérieur et que vous avez iptables, vous pouvez passez à l'étape suivante ... si vous avez un 2.4 et que vous ne l'avez pas (ça arrive, parfois), installez-le : sous Mandrake, urpmi iptables ; sous Debian, apt-get install iptables.
On va maintenant créer le script permettant de gérer le firewalling et le masquerading (partage de connexion). Pour cela, je vais utiliser l'éditeur de texte en mode console vim (en standard sur quasiment toutes les distribs). Pour ouvrir vim, tapez simplement vim ...
 |
Puis appuyez sur i pour passer en mode insertion de texte. Vous pouvez alors recopier le script ci-dessous, faire un copier coller ou le récupérer ici ...
#!/bin/sh
GREP=/bin/grep
AWK=/usr/bin/awk
SED=/bin/sed
IFCONFIG=/sbin/ifconfig
IPTABLES=/sbin/iptables
# Our complete stateful firewall script. This firewall can be customized for
# a laptop, workstation, router or even a server. :)
# change this to the name of the interface that provides your "uplink"
# (connection to the Internet)
UPLINK="ppp0"
# if you're a router (and thus should forward IP packets between interfaces),
# you want ROUTER="yes"; otherwise, ROUTER="no"
ROUTER="yes"
# change this next line to the static IP of your uplink interface for static SNAT, or
# "dynamic" if you have a dynamic IP. If you don't need any NAT, set NAT to "" to
# disable it.
NAT="dynamic"
# change this next line so it lists all your network interfaces, including lo
INTERFACES="lo eth0 eth1"
# change this line so that it lists the assigned numbers or symbolic names (from
# /etc/services) of all the services that you'd like to provide to the general
# public. If you don't want any services enabled, set it to ""
# SERVICES="http ftp smtp ssh rsync"
SERVICES=""
if [ "$1" = "start" ]
then
EXTIF="ppp0"
INTIF="eth0"
echo " External Interface: $EXTIF"
echo " Internal Interface: $INTIF"
echo " ---"
EXTIP=`$IFCONFIG $EXTIF | $GREP 'inet adr' | $AWK '{print $2}' | $SED -e 's/.*://'`
#NB : dans la ligne du dessus, il faut parfois mettre "inet addr" au lieu de "inet adr" ...
#si vous avez une erreur, faites le !
echo " External IP: $EXTIP"
echo " ---"
# Assign the internal TCP/IP network and IP address
INTNET="192.168.0.0/24"
INTIP="192.168.0.1/24"
echo " Internal Network: $INTNET"
echo " Internal IP: $INTIP"
echo " ---"
echo "Starting firewall..."
${IPTABLES} -P INPUT DROP
${IPTABLES} -A INPUT -i ! ${UPLINK} -j ACCEPT
${IPTABLES} -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
#enable public access to certain services
for x in ${SERVICES}
do
${IPTABLES} -A INPUT -p tcp --dport ${x} -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
done
########################################################################
#enable emule on server
${IPTABLES} -A INPUT -p tcp --dport 4662 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
${IPTABLES} -A INPUT -p udp --dport 4665 -m state --state ESTABLISHED,RELATED -j ACCEPT
${IPTABLES} -A INPUT -p udp --dport 4672 -m state --state ESTABLISHED,RELATED -j ACCEPT
#${IPTABLES} -A INPUT -p tcp --dport 4711 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
#######################################################################
${IPTABLES} -A INPUT -p tcp -i ${UPLINK} -j DROP
${IPTABLES} -A INPUT -p udp -i ${UPLINK} -j DROP
#explicitly disable ECN
if [ -e /proc/sys/net/ipv4/tcp_ecn ]
then
echo 0 > /proc/sys/net/ipv4/tcp_ecn
fi
#disable spoofing on all interfaces
for x in ${INTERFACES}
do
echo 1 > /proc/sys/net/ipv4/conf/${x}/rp_filter
done
if [ "$ROUTER" = "yes" ]
then
#we're a router of some kind, enable IP forwarding
echo 1 > /proc/sys/net/ipv4/ip_forward
if [ "$NAT" = "dynamic" ]
then
#dynamic IP address, use masquerading
echo "Enabling masquerading (dynamic ip)..."
${IPTABLES} -t nat -A POSTROUTING -o ${UPLINK} -j MASQUERADE
# uncomment these lines to enable edonkey ports be forwarded to your internal edonkey/emule client
PORTFWIP1="192.168.0.2"
#PORTFWIP2="192.168.0.3"
${IPTABLES} -A PREROUTING -t nat -p tcp -d ${EXTIP} --dport 4661:4662 -j DNAT --to-dest ${PORTFWIP1}:4661-4662
${IPTABLES} -A FORWARD -p tcp -i ${EXTIF} -o ${INTIF} -s 0.0.0.0/0 -d ${PORTFWIP1} --dport 4661:4662 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
${IPTABLES} -A PREROUTING -t nat -p udp -d ${EXTIP} --sport 4665 -j DNAT --to-dest ${PORTFWIP1}:4665
${IPTABLES} -A FORWARD -p udp -i ${EXTIF} -o ${INTIF} -s 0.0.0.0/0 -d ${PORTFWIP1} --dport 4665 -m state --state ESTABLISHED,RELATED -j ACCEPT
${IPTABLES} -A PREROUTING -t nat -p udp -d ${EXTIP} --dport 4672 -j DNAT --to-dest ${PORTFWIP1}:4672
${IPTABLES} -A FORWARD -p udp -i ${EXTIF} -o ${INTIF} -s 0.0.0.0/0 -d ${PORTFWIP1} --dport 4672 -m state --state ESTABLISHED,RELATED -j ACCEPT
####
${IPTABLES} -A FORWARD -p tcp --tcp-flags SYN,RST SYN -j TCPMSS --clamp-mss-to-pmtu
elif [ "$NAT" != "" ]
then
#static IP, use SNAT
echo "Enabling SNAT (static ip)..."
${IPTABLES} -t nat -A POSTROUTING -o ${UPLINK} -j SNAT --to ${UPIP}
fi
fi
elif [ "$1" = "stop" ]
then
echo "Stopping firewall..."
${IPTABLES} -F INPUT
${IPTABLES} -F FORWARD
${IPTABLES} -P INPUT ACCEPT
#turn off NAT/masquerading, if any
${IPTABLES} -t nat -F POSTROUTING
${IPTABLES} -t nat -F PREROUTING
fi
Quand vous avez fini, appuyez sur Echap, puis tapez les commandes suivantes :GREP=/bin/grep
AWK=/usr/bin/awk
SED=/bin/sed
IFCONFIG=/sbin/ifconfig
IPTABLES=/sbin/iptables
# Our complete stateful firewall script. This firewall can be customized for
# a laptop, workstation, router or even a server. :)
# change this to the name of the interface that provides your "uplink"
# (connection to the Internet)
UPLINK="ppp0"
# if you're a router (and thus should forward IP packets between interfaces),
# you want ROUTER="yes"; otherwise, ROUTER="no"
ROUTER="yes"
# change this next line to the static IP of your uplink interface for static SNAT, or
# "dynamic" if you have a dynamic IP. If you don't need any NAT, set NAT to "" to
# disable it.
NAT="dynamic"
# change this next line so it lists all your network interfaces, including lo
INTERFACES="lo eth0 eth1"
# change this line so that it lists the assigned numbers or symbolic names (from
# /etc/services) of all the services that you'd like to provide to the general
# public. If you don't want any services enabled, set it to ""
# SERVICES="http ftp smtp ssh rsync"
SERVICES=""
if [ "$1" = "start" ]
then
EXTIF="ppp0"
INTIF="eth0"
echo " External Interface: $EXTIF"
echo " Internal Interface: $INTIF"
echo " ---"
EXTIP=`$IFCONFIG $EXTIF | $GREP 'inet adr' | $AWK '{print $2}' | $SED -e 's/.*://'`
#NB : dans la ligne du dessus, il faut parfois mettre "inet addr" au lieu de "inet adr" ...
#si vous avez une erreur, faites le !
echo " External IP: $EXTIP"
echo " ---"
# Assign the internal TCP/IP network and IP address
INTNET="192.168.0.0/24"
INTIP="192.168.0.1/24"
echo " Internal Network: $INTNET"
echo " Internal IP: $INTIP"
echo " ---"
echo "Starting firewall..."
${IPTABLES} -P INPUT DROP
${IPTABLES} -A INPUT -i ! ${UPLINK} -j ACCEPT
${IPTABLES} -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
#enable public access to certain services
for x in ${SERVICES}
do
${IPTABLES} -A INPUT -p tcp --dport ${x} -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
done
########################################################################
#enable emule on server
${IPTABLES} -A INPUT -p tcp --dport 4662 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
${IPTABLES} -A INPUT -p udp --dport 4665 -m state --state ESTABLISHED,RELATED -j ACCEPT
${IPTABLES} -A INPUT -p udp --dport 4672 -m state --state ESTABLISHED,RELATED -j ACCEPT
#${IPTABLES} -A INPUT -p tcp --dport 4711 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
#######################################################################
${IPTABLES} -A INPUT -p tcp -i ${UPLINK} -j DROP
${IPTABLES} -A INPUT -p udp -i ${UPLINK} -j DROP
#explicitly disable ECN
if [ -e /proc/sys/net/ipv4/tcp_ecn ]
then
echo 0 > /proc/sys/net/ipv4/tcp_ecn
fi
#disable spoofing on all interfaces
for x in ${INTERFACES}
do
echo 1 > /proc/sys/net/ipv4/conf/${x}/rp_filter
done
if [ "$ROUTER" = "yes" ]
then
#we're a router of some kind, enable IP forwarding
echo 1 > /proc/sys/net/ipv4/ip_forward
if [ "$NAT" = "dynamic" ]
then
#dynamic IP address, use masquerading
echo "Enabling masquerading (dynamic ip)..."
${IPTABLES} -t nat -A POSTROUTING -o ${UPLINK} -j MASQUERADE
# uncomment these lines to enable edonkey ports be forwarded to your internal edonkey/emule client
PORTFWIP1="192.168.0.2"
#PORTFWIP2="192.168.0.3"
${IPTABLES} -A PREROUTING -t nat -p tcp -d ${EXTIP} --dport 4661:4662 -j DNAT --to-dest ${PORTFWIP1}:4661-4662
${IPTABLES} -A FORWARD -p tcp -i ${EXTIF} -o ${INTIF} -s 0.0.0.0/0 -d ${PORTFWIP1} --dport 4661:4662 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
${IPTABLES} -A PREROUTING -t nat -p udp -d ${EXTIP} --sport 4665 -j DNAT --to-dest ${PORTFWIP1}:4665
${IPTABLES} -A FORWARD -p udp -i ${EXTIF} -o ${INTIF} -s 0.0.0.0/0 -d ${PORTFWIP1} --dport 4665 -m state --state ESTABLISHED,RELATED -j ACCEPT
${IPTABLES} -A PREROUTING -t nat -p udp -d ${EXTIP} --dport 4672 -j DNAT --to-dest ${PORTFWIP1}:4672
${IPTABLES} -A FORWARD -p udp -i ${EXTIF} -o ${INTIF} -s 0.0.0.0/0 -d ${PORTFWIP1} --dport 4672 -m state --state ESTABLISHED,RELATED -j ACCEPT
####
${IPTABLES} -A FORWARD -p tcp --tcp-flags SYN,RST SYN -j TCPMSS --clamp-mss-to-pmtu
elif [ "$NAT" != "" ]
then
#static IP, use SNAT
echo "Enabling SNAT (static ip)..."
${IPTABLES} -t nat -A POSTROUTING -o ${UPLINK} -j SNAT --to ${UPIP}
fi
fi
elif [ "$1" = "stop" ]
then
echo "Stopping firewall..."
${IPTABLES} -F INPUT
${IPTABLES} -F FORWARD
${IPTABLES} -P INPUT ACCEPT
#turn off NAT/masquerading, if any
${IPTABLES} -t nat -F POSTROUTING
${IPTABLES} -t nat -F PREROUTING
fi
:w firewall
:q
Cela enregistrera le fichier sous le nom firewall, dans le répertoire courant, puis fermera vim.:q
Ensuite, il suffit de rendre le fichier firewall exécutable, et de le lancer :
chmod +x firewall
./firewall start
Normalement devrait s'afficher quelque chose comme :./firewall start
External Interface: ppp0
Internal Interface: eth0
---
External IP: votreIP
---
Internal Network: 192.168.0.0/24
Internal IP: 192.168.0.1/24
---
Starting firewall...
Enabling masquerading (dynamic ip)...
Internal Interface: eth0
---
External IP: votreIP
---
Internal Network: 192.168.0.0/24
Internal IP: 192.168.0.1/24
---
Starting firewall...
Enabling masquerading (dynamic ip)...
Voilà, le firewall est lancé ! Pour l'arrêter, il suffit de taper (attention, il faut être dans le répertoire où il y a le fichier) :
./firewall stop
Si vous voulez cutomizer le script : dans mon cas, l'ordinateur fait firewall/routeur/serveur pour les autres. Il posséde deux cartes réseaux, eth0 et eth1; eth0 est la carte connectée au switch, eth1 est connectée au modem ADSL. .L'IP locale de l'ordi est 192.168.0.1, et son nom est ceacy-net. Aucun service (web, ftp) n'est accessible depuis le net, mais ils le sont en local. L'ordinateur 192.168.0.2 est autorisé à utiliser eMule.
Ah, j'oubliais ! Ce firewall vous protège juste depuis l'extérieur : les programmes de vos ordis peuvent accéder au web ...